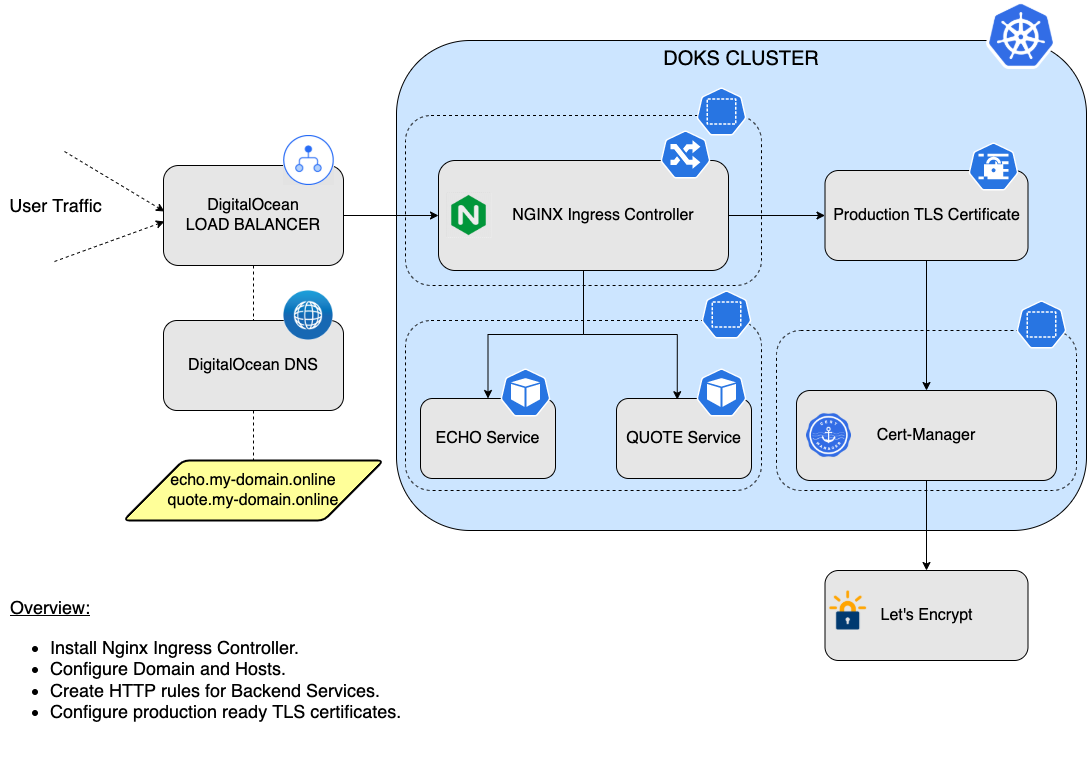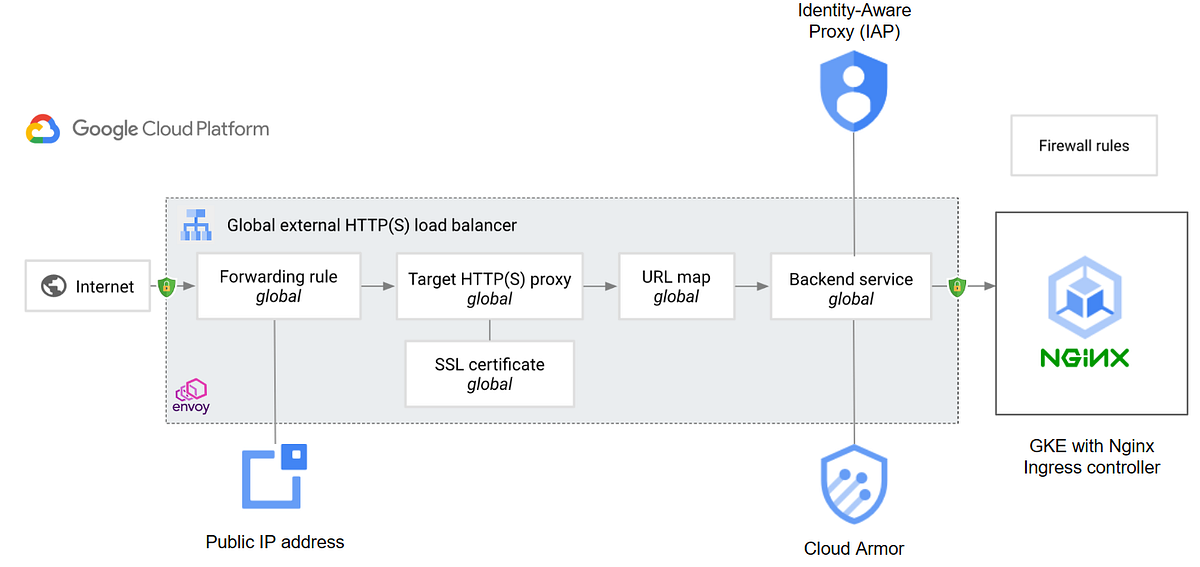
Secure your Nginx Ingress controller behind Cloud Armor or Identity-Aware Proxy (IAP) | by Mathieu Benoit | Google Cloud - Community | Medium

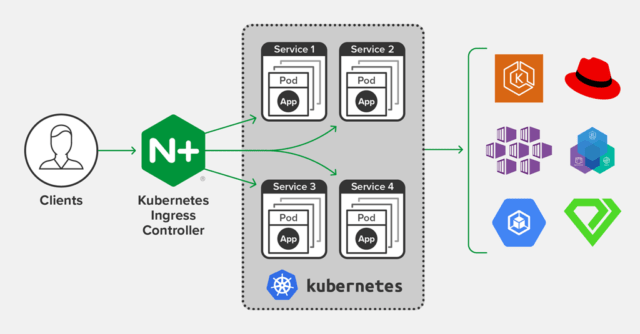
Multiple kong ingress controller or just one to different environments - General Discussions - Discuss Kubernetes

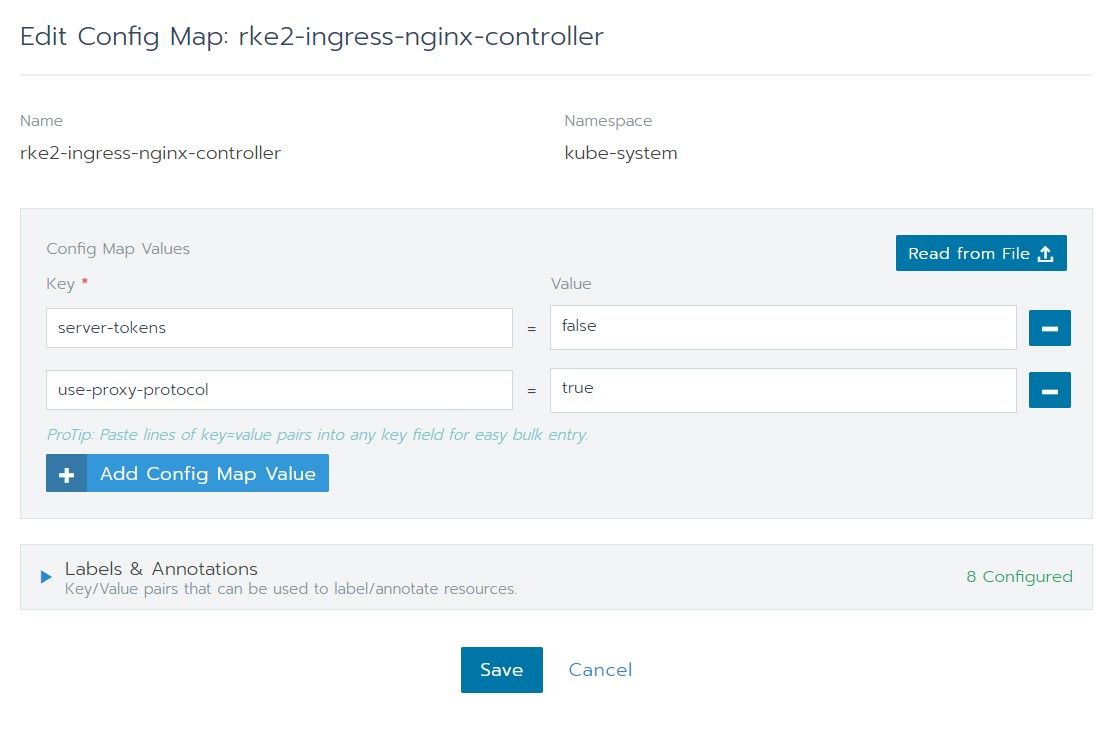
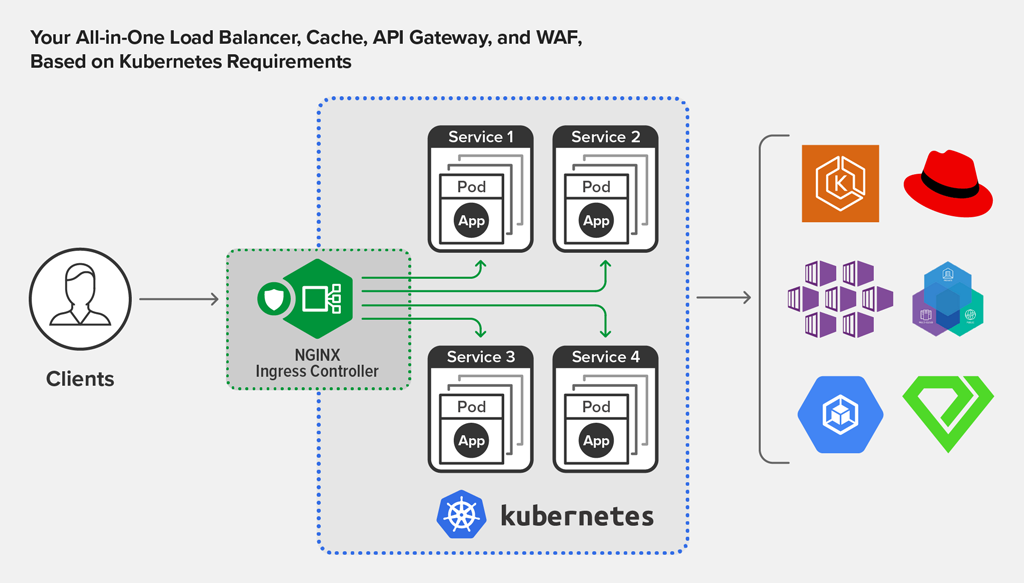
☸️ Kubernetes NGINX Ingress Controller: 10+ Complementary Configurations for Web Applications - DEV Community

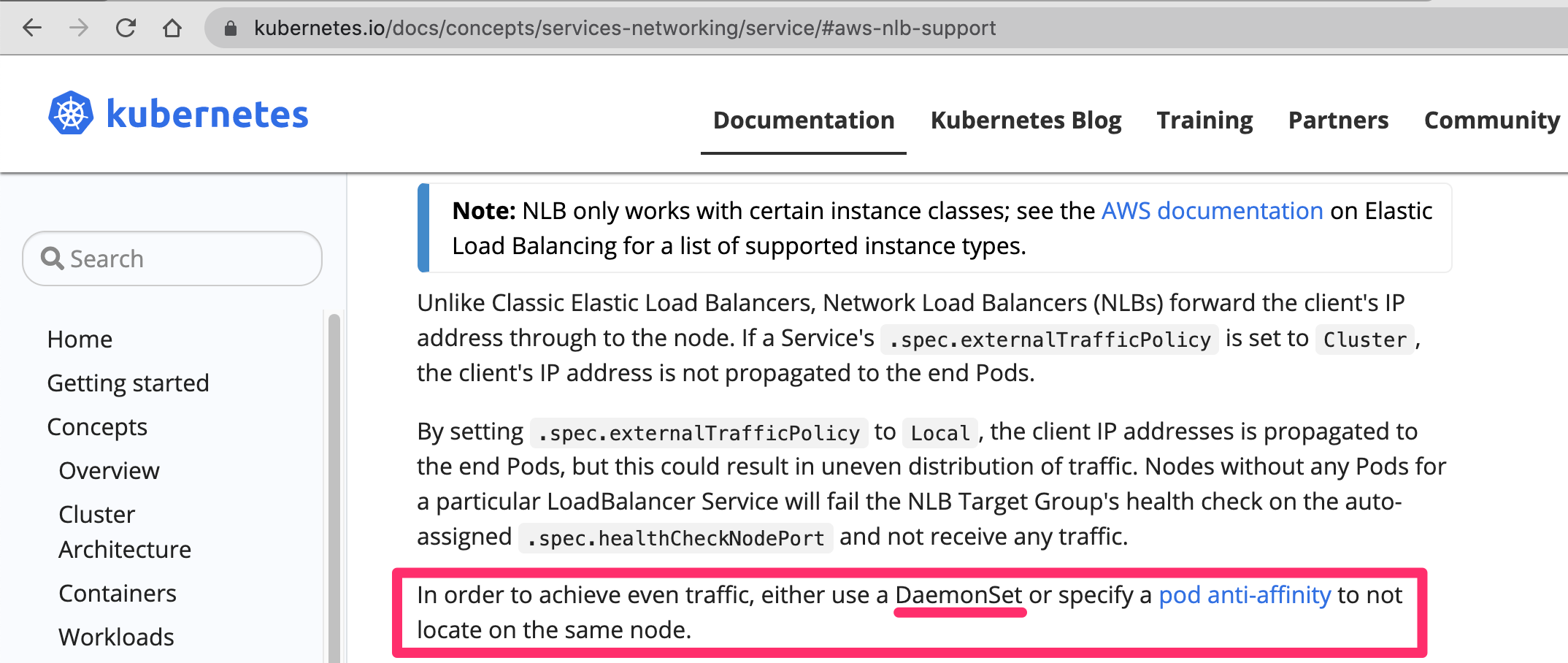
Injected nginx ingress controller doesn't have access to the remote client IP · Issue #3403 · linkerd/linkerd2 · GitHub